Searching for a specific string like qarovviraf153 can feel very confusing. You might see this code in a technical log or on a social media profile. Many people feel a sense of worry when they find a term they do not know. You may be asking if it is a virus, a secret password, or just a random mistake. This uncertainty can make you feel rushed to find an answer. It is a common frustration to want clarity in a digital world that often feels too complex. This guide will help you understand exactly what identifiers like this mean. We will show you how to stay safe and how to manage your own digital footprint with ease.
Why Technical Identifiers Like qarovviraf153 Exist Today
The internet is a very big place with billions of users. Because there are so many people, simple names like “John” or “Sarah” are all taken. This is why we see strings like qarovviraf153. These codes are unique. They act like a digital fingerprint. In technical systems, these strings help computers find the right data quickly. Without these unique codes, the internet would be a mess of mixed-up files.
When you see a code that looks random, it usually serves a structural purpose. It ensures that no two accounts or files have the same name. This prevents errors and keeps your information separate from others. Understanding this helps take away the mystery. It is not a secret code meant to trick you. It is a tool for organization.
Common Frustrations with Unknown Digital Codes
Many users face the hurdle of seeing a code and not knowing its source. You might feel a bit of fear that your privacy is at risk. This is a very normal way to feel. Digital security is important. When a string like qarovviraf153 appears in a search, it often leads to empty pages or technical forums. This lack of information is the primary reason for user frustration.
To solve this, you should first look at where you found the code. If it is on a social media site, it is likely just a creative username. If it is in a system folder, it is probably a temporary file name. Knowing the context is the first step to feeling more in control.
How to Solve the Mystery of Digital Strings
If you are still worried about a specific string, you can follow simple steps to gain peace of mind. First, do not click on suspicious links that promise to “reveal” the meaning of a code. These are often traps. Instead, use a trusted search engine to see if the code is linked to known software.
Most unique identifiers are “placeholders.” This means they stand in for something else until a real name is given. For example, a website might use qarovviraf153 as a temporary ID for a new page. Once the page is ready, the name changes. If you find such a code, it is often best to leave it alone unless it is causing a technical error on your device.
Protecting Your Online Presence and Identity
Your digital identity is a collection of all the names and codes linked to you. Managing this well is a great way to reduce stress. You should aim to be consistent with your usernames. Using a unique string that you create can actually help your privacy. It makes it harder for strangers to find your real-world identity.
However, you must also be careful. If you use a code like qarovviraf153 across every site, it becomes a trail. A person could follow that trail to see everything you do online. This is why experts suggest using different names for different types of sites. Use one name for games and another for professional work. This separation keeps your life organized and safe.
The Role of Alphanumeric Names in Modern Tech
Codes that mix letters and numbers are called alphanumeric. These are very strong because they have many combinations. A code like qarovviraf153 is much harder for a computer to guess than a simple word. This is why many systems require you to add numbers to your passwords or usernames.
These codes also help with automation. Robots and AI programs use these identifiers to sort through millions of items in a second. They do not care if a name sounds pretty. They only care that the name is unique. As we move into a future with more AI, we will see even more of these unique strings. Learning to live with them is a key part of digital literacy.
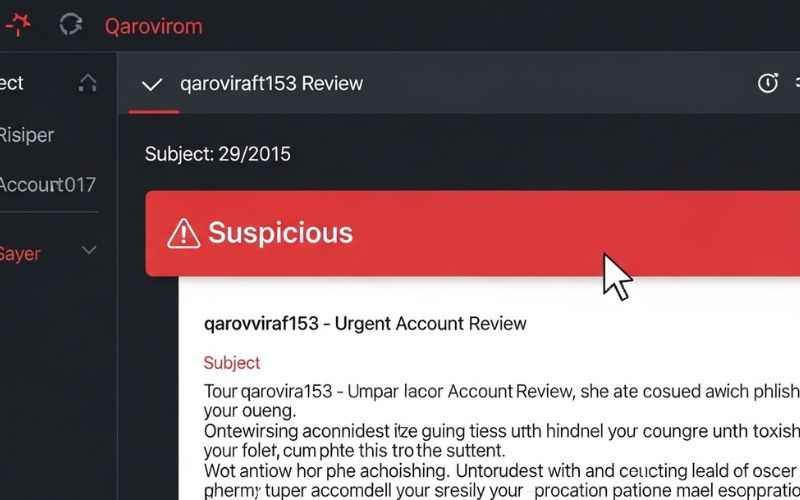
Dealing with Spam and Security Risks
Sometimes, scammers use strange codes to get your attention. They know that people are curious. You might get an email with a subject line that includes a code. Their goal is to make you click. If you see a code like qarovviraf153 in an email from someone you do not know, delete it.
Real technical codes stay in the background. They do not usually ask you for money or passwords. If a code “talks” to you or asks for your help, it is likely a scam. Staying calm and skeptical is your best defense. You have the power to ignore these digital distractions and stay focused on what matters.
Why Precision Matters in Digital Systems
Computers are very literal. They need exact instructions. If a database is looking for one specific user, it cannot guess. It needs a tag like qarovviraf153 to find the exact match. This precision is what allows us to shop online, send messages, and save our progress in games.
Even if the code looks like “noise” to us, it is “music” to the computer. It tells the machine exactly where to go. This efficiency saves time and energy. It also reduces the chance of a computer accidentally deleting the wrong thing. We can be thankful for these codes because they keep our digital world running smoothly.
Managing the Confusion of New Technology
Technology moves very fast. It is okay if you do not understand every term right away. Many people feel left behind. The key is to ask questions and look for simple explanations. You are doing the right thing by reading this guide.
When you see something like qarovviraf153, think of it as a label on a box. You do not always need to know what is inside the box to know that the label helps the post office deliver it. Most digital identifiers are just labels. They help the internet “mail” your data to the right spot.
Tips for a Better Digital Experience
To make your time online easier, try these simple tips:
- Use a password manager to keep track of your names and codes.
- Do not reuse the same unique identifier for sensitive accounts.
- If a code looks scary, search for it on a safe site like a tech news blog.
- Remember that most random strings are harmless system files.
- Keep your software updated to ensure your identifiers are handled correctly.
By following these steps, you can turn a confusing moment into a learning moment. You will feel more confident as you navigate different websites and apps.
The Human Side of Digital Identifiers
We often forget that humans are the ones who build these systems. Even a code like qarovviraf153 was likely set up by a person or a person’s program. We use these tools to solve human problems, like how to store too much data.
Sometimes, people use these codes as a way to express themselves. A unique name can be a badge of honor in a gaming community. It shows you were there first. It shows you are unique. There is a bit of art in finding the perfect code that no one else has.
Solving Technical Errors Related to Unknown Strings
If a code like qarovviraf153 shows up in an error message, it is a “stop sign.” It tells the technician exactly where the problem is. If your computer freezes and shows a code, write it down. You can give this code to a repair person.
This saves them a lot of time. Instead of looking at the whole computer, they can go straight to the area marked by the code. In this way, these “mysterious” strings are actually very helpful. they are like road signs that help experts fix your tech problems faster.
Understanding the Growth of Online Communities
As more people join the internet, the need for unique tags grows. Communities use identifiers to track who is a member and what they have done. A name like qarovviraf153 might represent a long history of posts and help in a forum.
When you see a string, you are seeing a part of a growing digital family. Every code represents a point of connection. While it may seem cold or robotic, it is actually a sign of a very busy and social digital world. We are all connected by these strings of data.

You May Also Like: Finding amyregal4711: The Ultimate Guide to Solving Your Search Frustrations
Final Thoughts on Navigating Digital Identity
You now have the tools to understand strange strings like qarovviraf153. You know that they are usually just tools for organization and security. You understand that they help computers be precise. Most importantly, you know how to stay safe and calm when you find one.
The internet does not have to be a scary or confusing place. With a little bit of knowledge, you can feel like an expert. You can manage your identity, protect your privacy, and solve technical mysteries. You are in charge of your digital journey.
Frequently Asked Questions About qarovviraf153
Is qarovviraf153 a sign of a virus on my computer?
Usually, it is not. Most random-looking strings are just identifiers for files or user accounts. If your computer is running normally, you likely have nothing to worry about.
How can I find out where a digital code came from?
Look at the context. If it is in an app, check the app’s help section. If it is on a website, it might be a username. Only search for the code on trusted websites.
Why do some usernames have so many numbers at the end?
Because many names are already taken, platforms suggest adding numbers. This ensures that your name is unique and the system can identify you correctly.
Should I be worried if I see my own name as a code?
No. Many systems convert real names into codes to protect privacy. This is a standard way to keep your personal data safe from hackers.
Can I delete files that have strange names like qarovviraf153?
Be careful. If the file is in a system folder, deleting it could cause an error. It is best to use a “disk cleanup” tool that knows which files are safe to remove.
Disclaimer:
The information provided in this article regarding qarovviraf153 is for educational and informational purposes only. While we strive for accuracy, digital identifiers and technical strings can evolve rapidly. This content does not constitute professional technical or legal advice. Use of this information is at the reader’s own risk. We are not responsible for any technical issues or data loss resulting from the application of these tips.

Emma Rose is a simple, clear, and helpful writer at Blogtime. She enjoys creating easy-to-read articles on tech, lifestyle, travel, and everyday tips. Emma’s goal is to make learning simple for everyone by explaining ideas in friendly and easy words. When she’s not writing, she loves reading, exploring new places, and finding inspiration in everyday life.
